We will join this May 22-24 fellow smart lighting leaders at the UMQ’s Assises 2024 annual conference held in Montréal
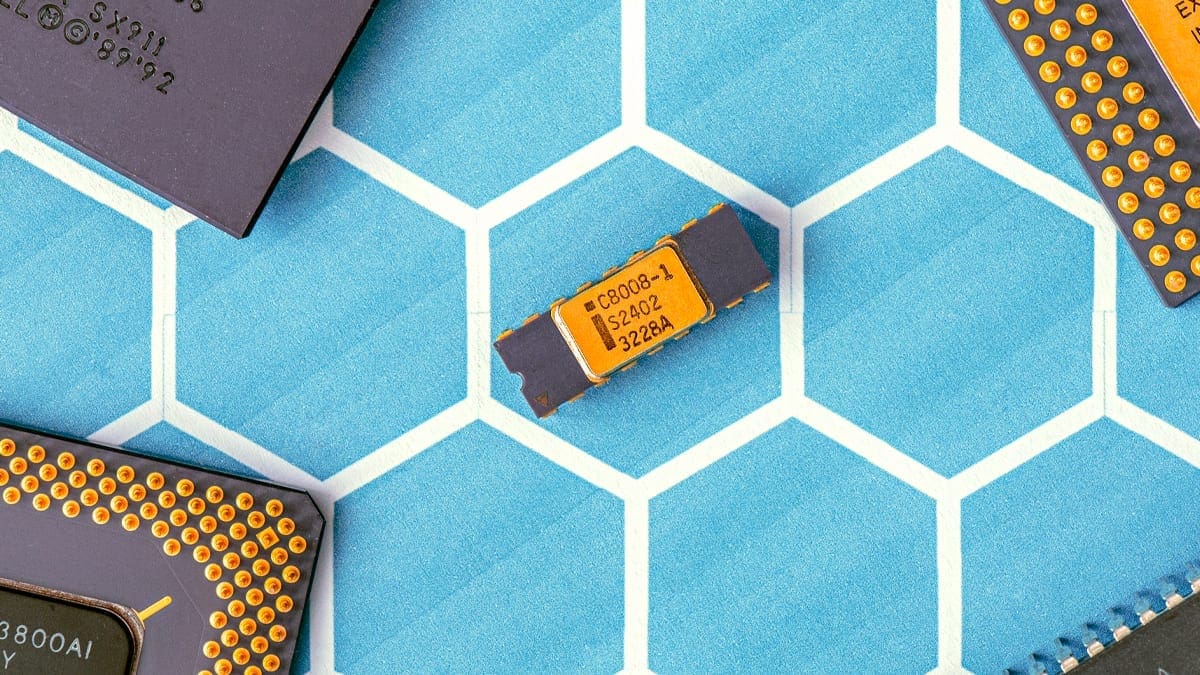
Yocto & Wind River: The Most Advanced Embedded Linux Distribution
Intelligence at the edge is in many cases an “unmissable” architecture requirement in today’s IoT type product. Some markets and verticals highlight the importance of this requirement driven by performance, compliance & licensing, scalability and security.
Latest market opening driven by 5G even push this requirement to get:
- More CPU power to the edge (autonomous driving, assisted tele-medical device, Advanced IoT)
- More connectivity (protocol stack, encryption, commissioning)
- More complex processing requiring complex software modules (multifactor identification, dynamic authentication)
The Yocto project defines itself as ‘’an open source collaboration project that helps developers create custom Linux-based systems regardless of the hardware architecture’’. This project also provides technical flexibility to fit the needs of any company in any industry, with the scale to fit the expansive needs of embedded devices, machines, systems, and IoT architectures. In other words, it allows to assemble a custom footprint of Linux for a targeted hardware with selected libraries to create various size or footprint OS. Even more, it allows to maintain it efficiently for various library versions and various hardware through time.

Since the last 2-3 years, Wind River maintains a serious distro giving a new level of maturity oriented on:
- Security (security patch, vulnerability testing and protection mechanism)
- Compliance (licensing)
- Performance (Real Time, hardware real time build switch)
Most of the work performed by Wind River gravitates towards three main categories:
- Open Source Software Compliance Artifacts
- Security Vulnerability Protection
- Support and Maintenance
Wind River has changed its distro name and definition several times from Pulsar to “WR Linux 10.0” to produce a “Military Grade Linux” allowing to reduce cost of development, maintenance, legal fees and certification. They created multiple security protection mechanisms with no trade off on performance, as per example:
- Authentication to ensure that any module running is keyed
- From developer commit verification, making sure any source is not tampered
- Bake kernel image
Learning to use the Yocto framework and tools is a heavy curve over Linux knowledge, but once assimilated it allows to efficiently, securely, repeatedly and consistently develop and maintain products. Nonetheless, this framework is recommended for mature IoT product markets or for those who have spent an important amount of time manually maintaining their Linux operating system.
Bibliography:
- Wind River Linux – Open Source Leadership: https://windriver.com/products/linux/open-source-leadership/
- The Yocto project: https://www.yoctoproject.org/
- Dimonoff Open Source Project Contributions: https://www.dimonoff.com/news/contribution-to-open-source-projects/
- Making the Grade with Cybersecurity, Linux, and the Intelligent Edge: https://resources.windriver.com/linux/making-the-grade-with-cybersecurity-linux-and-the-intelligent-edge
- GitHub Contributions (Wind River Labs): https://github.com/WindRiver-Labs/wrlinux-x
- Common Vulnerabilities and Exposures: https://en.wikipedia.org/wiki/Common_Vulnerabilities_and_Exposures
You have an idea for a project and need our expertise to achieve it?
Contact our experts!
Author: Eric Dusablon
VP Business Development. Projects are driving my career. Managing successfully complex teams and complex projects with key developers is a great feeling. Realizing the best solution to a problem is the only reward. If it is new, if it helps somehow to resolve a problem, if there is a balance between challenge and budget. It is made for me!